How I Used Mac Addresses to Identify All the Smart Devices On My Network

⚠️ This was originally posted on October 26, 2016. The information may be outdated!
Like many tech-savvy thirty-somethings my household has acquired quite a few Wi-Fi-connected devices over the past few years:
- Fitbit Aria Wi-Fi scale
- Wireless printer
- Smart thermostat
- Apple TV/Roku
- Smart HDTV
- Wi-Fi baby monitor
- Wi-Fi security cameras
- Smart phones, tablets, computers
- etc.
Our network had gradually become highly populated with devices, and I didn’t even notice. When I upgraded our router a while back I used the same SSID and password so I didn’t have to reconfigure any Wi-Fi connected devices (although I did set up a separate 5Ghz network for video streaming for a few devices). It has literally been years since I had to do any kind of inventory on what devices we had on our Wi-Fi network.
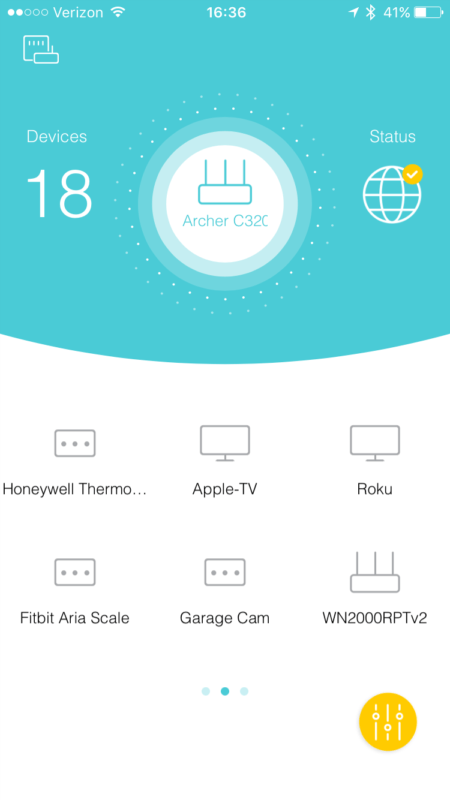
With IoT device vulnerabilities becoming more commonplace I wanted to make sure nothing looked fishy on my Wi-Fi network. My router’s web interface was pretty good, but for fun I installed TP-Link’s Tether app on my iPhone to try it out. Once I logged into my router via the app it showed a list of connected devices. I recognized many right away, but there were several that I didn’t recognize with names like “Unknown” or “NP-<bunch of characters>.” In my head I couldn’t reconcile the number of devices on my network with the number of devices that I thought should be connected, so I decided to dig deeper.
I started looking for a way to identify the devices I didn’t recognize, and that led me to http://www.coffer.com/mac_find. I was able to type in the MAC address for each device on the website and see who the vendor was (the Tether app helpfully displays the IP and MAC addresses for each device). If the vendor name didn’t make it obvious, a brief Google search found the answer. For example, the Fitbit Aria scale’s MAC address came up with “GainSpan” as the vendor. That led me to this article that confirmed what it was. If the MAC address didn’t provide good information, I tried searching the device name itself. One device was named “NP-<serial number>” and so I searched “network device starts with np-” and the first result for me led to a forum post on Roku’s website that confirmed this was my Roku.
As I identified devices, I updated their names in the Tether app so I don’t have to remember them in the future. I’ll be sure to update the list as new devices are added going forward.
One more recommendation: try running a scan with https://iotscanner.bullguard.com/ to see if any IoT devices on your network could be vulnerable.
Comments
Comments are closed